In this post I want to share with you a list of tips and tools that I feel have boosted my day-to-day productivity on the computer. The title suggests this is only for IT professionals. However I can’t see why power users can’t appreciate what’s here too. You may already have different tools that achieve similar, or better, functionality, so drop a comment below or tweet your tip on Twitter using the hashtag #EveryDayITPro.
Over the weekend I ran into a weird issue that I hadn’t seen before. I was upgrading half of the Distribution Points for a client who’s ConfigMgr was in need of some TLC. I’ve been working on getting their overall infrastructure healthy and that includes upgrading their DPs from Windows Server 2012 to Windows Server 2016 (and eventually 2019). Once I started the upgrades I worked on other things while checking in on them periodically.
Introduction Introduced with ConfigMgr 2002, the “Task Sequence as an application deployment type” feature is available in pre-release. That means it is still in active development and can contains bugs. Using a Task Sequence (TS) as a deployment type allows for more complex installation process that can even contains reboot. And as it is a Task Sequence, you can also benefit from many other feature like the use of TS variables.
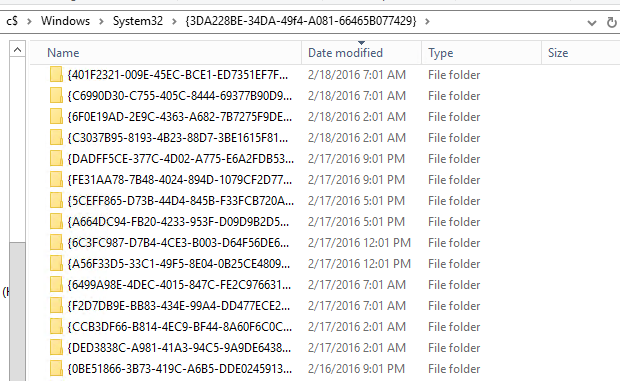
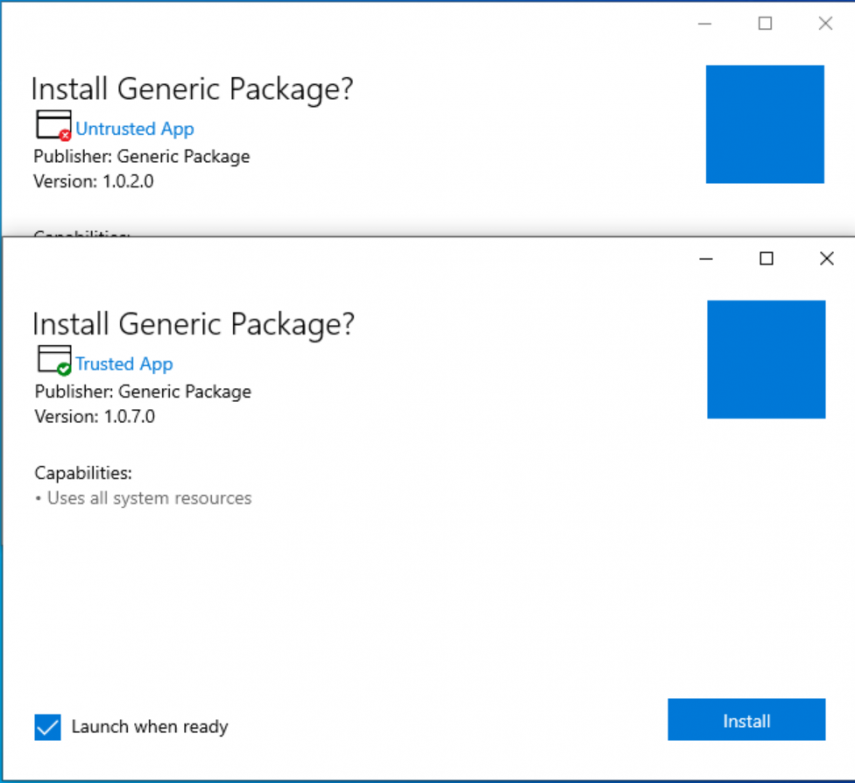
Why would I want to use MSIX and what is it? MSIX is a Windows app package format that provides a modern packaging experience to all Windows apps. The MSIX package format preserves the functionality of existing app packages and/or install files in addition to enabling new, modern packaging and deployment features to Win32, WPF, and Windows Forms apps. Do you have a bloated application? Maybe one or two that are so old it doesn’t even have any install parameters?
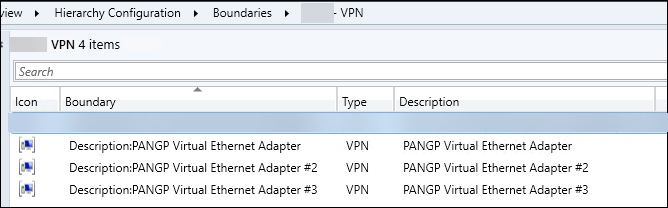
Like many, I was very excited that the new Configuration Manager 2006 release included a huge improvement for remote devices by adding a new VPN Boundary type. “Finally! I don’t have to constantly bug my Network Engineers as to which IP pools are being used for which VPN appliances.” Create A New Boundary In the Admin Console, navigate to the Administration Node and open up Hierarchy Configuration and right-click on Boundaries
The Problem So I was walking on the beach and noticed that OneDrive wasn’t syncing anymore on my AzureAD joined laptop. I later learned that my endpoint administrator, Adam Gross, had enabled Allow syncing only on computers joined to specific domains in the OneDrive admin portal. which effectively blocked my AzureAD device 🙁 Which resulted in this message on my corporate device Our Legacy AD joined devices were fine, but all of our Azure AD joined devices got the above error.
Introduction I recently wrote PSCMContentMgmt which provides a simple and effective workflow for managing your MEMCM distribution points. Here are some of the things you can do with it: Query content objects which are distributed to distribution point(s) or distribution point group(s) Compare content objects distributed to distribution point(s) or distribution point group(s) Find content objects in a “distribution failed” state for all or selective distribution points Remove, distribute or redistribute content objects returned by any function to distribution point(s) Find an object in your site by searching on any arbitrary ID (useful when reading logs and want to know what object an ID resolves to) Migrate a distribution point’s content to a new/different distribution point by exporting its content library to prestaged .
The other day, I logged on to a jump server and, while investigating an unrelated issue, I noticed the BG Info background showed the Last Reboot as March 1st, 2020. “That can’t be right,” I thought. “We have weekly maintenance windows to reboot these servers.” As I opened an old stand-by function from my stash (originally posted here: https://gallery.technet.microsoft.com/scriptcenter/Get-RebootHistory-bc804819 in 2015) and ran it, I was a bit annoyed at how SLOW it was.
Months after we issued students and faculty 600+ unmanaged off the shelf laptops (no AD, no Azure AD, no Intune, no ConfigMgr) to get them off and running temporarily during this pandemic, my co-worker and I were tasked with figuring out how to bring these machines under some form of management. We did not have these machines in ConfigMgr or have the hardware hashes uploaded into Intune, so we had some work ahead of us.
The Problem For any new machines ordered from a vendor such as Dell that get enrolled into Autopilot you get the basic device info enrolled but nothing defining that would let it get auto-enrolled into a dynamic group easily. Purchase Order ID is included in every order we receive from Dell however I don’t want to have to add that Purchase Order ID into the dynamic device query every time a new machine gets added.