About 6 months ago I moved to a new company and, after having been a Windows Admin for basically the previous decade, I’m now a de facto Mac Admin, though I don’t consider myself an expert in macOS or iOS yet. I’m learning quickly, but I also feel like I may have some more conservative views for managing Macs that definitely spill over from my Windows & ConfigMgr days. When I was hired, I knew going in that my first major project would be migrating the entire company from one MDM (Meraki Systems Manger) to another as part of an effort to bring all endpoint management under in-house IT.
In this post, I will show you the steps required to preinstall Windows Terminal (or any signed MSIX Application) to a generalized Windows image. The goal of this post is to create an image of Windows 10 that can be deployed to an IT department that already has Windows Terminal baked into the OS, instead of having to go out to the Windows Store and install it yourself NOTE: This only works on a generalized image.
Introduction In this post, I’ll give you some background information and show you how to utilize the Microsoft Graph API to bulk update Azure AD user photos. If you’d like to skip the background information and get straight to the nitty-gritty, click here. Background I work at a private K-12 school in the United States. Like many schools out there, we have scheduled portraits once a year for students and staff.
Script Introduction This post will go through the steps required to create and deploy a password expiration script to run daily and send an email to all users whose passwords will expire in a set number of days. Scheduled tasks are the recommended implementation for this password expiration script. There are probably other ways to implement this script; however, this script targets scheduled tasks in Windows. 1 2 3 4 #Clear any stored errors $error.
App deployment for any computer, Windows or Mac, can be challenging. Widely used apps like Google Chrome are well-developed with options to automate and configure using scripts, MDM config profiles, or even back one-liner terminal commands. When you encounter an app that has little-to-no documented parameters or configurations, it can be frustrating. I choose to look at it as a challenge. Using any tools or ideas available, it’s easy for me to become engrossed in finding an automatable solution.
I’m deploying Azure Virtual Desktop currently for a client and they want a “general shared desktop” pool that will have a bunch of core apps including Microsoft 365 Apps installed. However, not every user will be licensed for Visio or Project, and only a very select few users are allowed to use Publisher, and fewer still allowed MS Access (They’ve signed contracts so that if they dare create anything in Access, they have to support it for free till day they die, then their next of kin take over support.
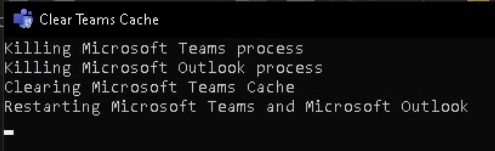
Microsoft Teams Cache, we’ve all been there in the last year and a half. Microsoft Teams is working fine, then it’s not. What happened? I restarted Teams and it’s still acting weird. Well, Teams is an interesting app when it comes to its cache. It relies heavily on it. I personally do not know all the ins and outs of the Teams cache, but I too know all too well that it is a pain in the butt when it goes awry.
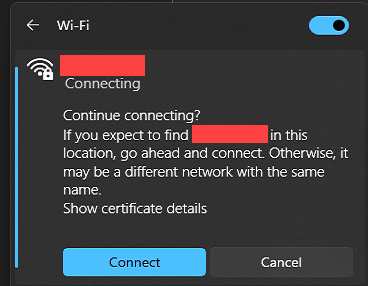
As of Windows 11, we noticed that we were getting prompted to continue connecting to a network that we’d never had a problem with before. It’s already defined in group policy, so this new behavior is puzzling and annoying. The certificate in question is for the NPS/Radius server our network uses to validate credentials for the wifi. Continue Connecting I really had no idea how to even begin googling for this problem, but while talking to some of my fellow nerds on the Winadmins Discord server, tossing around some ideas on what could be causing this, looking to see whether there was a problem with the certificate, etc.
Intro So you’ve started rolling out Windows 11 to your endpoints, and your users got confused and upset over the consumer teams apps that is installed? Understandably you wish to do something about this. (╯°□°)╯︵ ┻━┻ No worries mate, Intune Proactive Remediations to the rescue! The Solution The code below fixes two things. It removes the chat by writing the registry key that disables it the TaskbarMn DWORD controls this Then it simply uninstalls the appx package for the consumer teams app, note that this has no effect on the regular teams app.
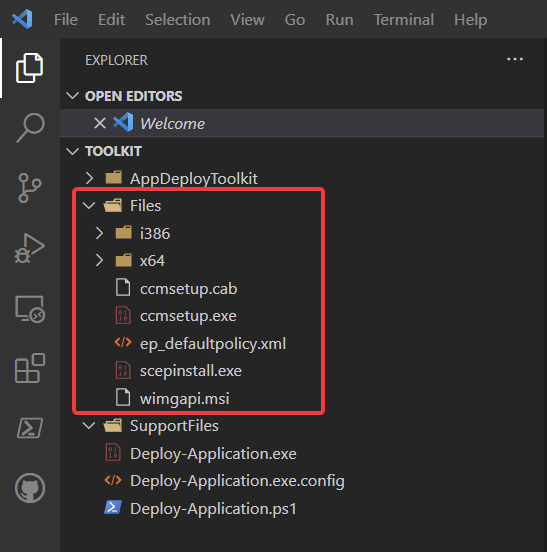
Hey Siri, Write A Blog Post For Me THE CONTENTS IN THIS POST IS EXPIRED, DO NOT USE THIS ANYMORE This method of installing the Configuration Manager Client during Autopilot is no longer needed Please use the new autopilot into co-management feature. Autopilot into Co-Management Overview Installing the SCCM Client During Autopilot EXPIRED CONTENT BELOW Deploying the Configuration manager client is usually pretty simple. the procedure is well documented. However there are issues if you plan on installing the CM client during Autopilot using the officially suggested methods